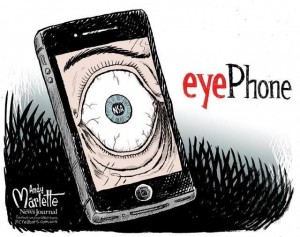
The funny pictures and videos we now call “memes” are all over the internet. While most memes may have the same format and pictures, the text often changes to create humor out of a generally more serious topic. When the 2013 NSA/Snowden scandal happened, it became the subject of many memes/videos on the web. One might think making a funny picture out of an issue as serious as privacy and surveillance is innappropriate, but it’s just a way of helping us cope. It reminds us that while these awful things may be happening, we can find humor in the situation that may give us hope or encouragement to intervene and stand up for what we think about what’s going on in the world around us.

The issue of privacy and surveillance is something that affects everybody. Bob Sullivan in his article “Privacy under attack, but does anybody care?” said “Privacy is like health: When you have it, you don’t notice it. Only when it’s gone do you wish you’d done more to protect it.” Everyone has many things that they don’t want the rest of the world to know about and that’s exactly why were given the right to keep our personal lives private. As the years go on, that right we were promised seems to be slowly eroded. Our phone calls are monitored, surveillance cameras are everywhere we look, and our cell phones can tell anyone where we are at any moment. These are all things that are scary, invasive, and unsettling. So why do we joke about them? Inserting humor in a serious situation is a very effective away to apply that situation to our own lives. Seeing a meme we recognize that includes text or a picture about privacy and surveillance allow us to relate that issue to our own lives and realize that it does affect us personally.
How do we go on living our daily lives without being in constant fear and suspision? We do it by turning fear into laughter. That’s not to be mistaken with taking the situation lightly..that’s not the purpose of the internet memes. Creating humor in a seemingly helpless situation allows us to know the issue and make the connection to our own lives, and that is exactly why joking about the situation on the web is a coping device for so many. While we may not google search “surveillance memes” when we’re feeling a bit uneasy about drones flying about, seeing a meme on our twitter feeds about the situation allows us to see the situation, imitate the feelings it gives, and respond/share positively. Richard Dawkins said: “Memes propagate themselves in the meme pool by leaping from brain to brain via a process which, in the broad sense, can be called imitation.” Everyone knows what is happening with privacy and surveillance and seeing those pictures may help people to realize how rediculous the situation is from an outside perspective and suddenly feel inclined to do or say something about it to their peers or the government/corporation itself.
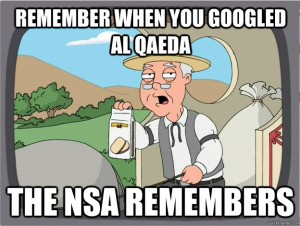
Lightening up a serious situation with humor has been around long since the internet. Television involves cartoons addressing serious situations and newspapers involve political comics creating an enjoyable spin on the most recent scandals. While television and newspaper memes are easily accessable to us, internet memes are avialable to us almost immediately. Paul Brewer, associate director for research at the University of Delaware’s Center for Political Communication, says “Many of us are using television, social media, smartphones and tablets all at the same time as we take in the debates, by the time the debate is halfway over, there’s already a Tumblr site full of memes.” Memes are an extremely effective way to not only make people laugh, but spread the laughter around the World Wide Web quickly.
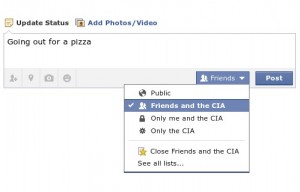
As humans, we have certain ways of dealing with situations we feel like we can do nothing about. The government and big businesses are the main ones involved in invading the privacy in our lives, and as a single person we feel helpless against those powers. Seeing and sharing a funny picture about privacy and surveillance allows us to relate to the situation ourselves, and sharing that picture with our friends allows us to spread the word. Pal Gil, an internet basics expert said, “A meme with political humor attached to it can virally spread awareness of an issue, or can help to reinforce growing attitudes and prejudices.” Internet memes on privacy and surveillance are informative, they’re effective, and they’re down-right hilarious.
Neuman, Scott. “Political Memes: Fast, Cheap, and Out of Control?” NPR. 24 Oct. 2012. Web. 11 Oct. 2014. .
Gleik, James. “What Defines a Meme?” Smithsonianmag.com. Smithsonian Magazine, 11 May 2011. Web. 11 Oct. 2014. .
Sullivan, Bob. “Privacy under Attack, but Does Anyone Care?” NBC News. 17 Oct. 2006. Web. 11 Oct. 2014. .
Gil, Paul. “Why Would You Ever Create an Internet Meme?” About Technology. About.com. Web. 11 Oct. 2014. .